Cybersecurity has spent decades reacting to attacks after the damage is already done. Now, according to Dmitry Volkov, CEO ...

Australia’s top cyber leaders have said that cyberattacks are no longer hypothetical, isolated events targeting only big ...

Buying AI tools is easy. Building the infrastructure to support them is not as easy.
According to John Hines, Senior ...
No results found.
No results found.
Today, Cognizant announced an expanded strategic alliance with CrowdStrike to help enterprises secure artificial ...
Lenovo today announced it is delivering a near real-time AI-powered infrastructure platform for the FIFA World Cup 2026™ ...
Gigamon has partnered with Splunk, a Cisco company, to deliver a new approach to accessing and analysing distributed data ...
No results found.
No results found.
No results found.
No results found.
Business News ↓
TrendAI™ joins Anthropic’s Project Glasswing. Collaboration will support efforts to identify and remediate software ...
Today, Cognizant announced an expanded strategic alliance with CrowdStrike to help enterprises secure artificial ...
Gigamon has partnered with Splunk, a Cisco company, to deliver a new approach to accessing and analysing distributed data ...
No results found.
Cyber threats have moved to mobile communications, where identity, metadata exposure, and AI impersonation undermine trust.
Government in Constant Motion
Federal government work now extends beyond offices to secure facilities, international ...
Mission-certified communications deliver secure, unified support in high-stakes operations.
No results found.
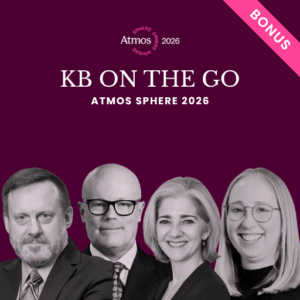
In this episode of KB on the Go, recorded at Atmos SPHERE 2026, Karissa Breen brings together two conversations united by ...

Australia’s energy sector may be further ahead than most industries when it comes to cybersecurity preparedness, but ...

Introduction
For years, digital assets have been spoken about in extremes. Either as the future of finance, or as a ...
No results found.

Global enterprises are under mounting pressure to rethink how and where they manage data. Cross-border transfers, cloud ...
Introduction
Organisations must move beyond reactive security postures and embrace data-driven decision-making as the ...
Introduction
Building a strong information security posture is no longer optional. For tech executives tasked with ...
No results found.

KBI.Media is proud to announce a landmark partnership between KBKast, the flagship security podcast for leadership, ...

Toby Jones, Founder of TJC, speaks on the often misunderstood convergence between government and industry. The ...

As far as cybersecurity networks go, 2020Partners stands out—a private, non-commercial coalition of senior security ...
No results found.
Markets & Trading
YOUR SECURITY NEWSFEED
The KBI Dossier
The Cybersecurity news feed delivered straight to your Inbox.
Technology News ↓

Across Australia, the acceleration of AI-assisted and automated software development has created increased risk to the ...

Quantum Key Distribution (QKD) has long been considered difficult to scale because it requires dedicated QKD appliances. A ...

Cybersecurity industry analyst Richard Stiennon at IT-Harvest says artificial intelligence is reshaping the future of ...
No results found.

Buying AI tools is easy. Building the infrastructure to support them is not as easy.
According to John Hines, Senior ...

Across Australia, the acceleration of AI-assisted and automated software development has created increased risk to the ...

Cybersecurity industry analyst Richard Stiennon at IT-Harvest says artificial intelligence is reshaping the future of ...
No results found.

The next cyberattack could be human, or a human engineering an AI from the outside, or an AI engineered from the inside. ...

Cyber incidents start quietly, which looks like a compromised credential, a malicious attachment, an employee doing what ...
I was researching cyberattacks, and a common theme popped out. “We had an unprecedented cyberattack… and we shut down our ...
No results found.

Across Australia, the acceleration of AI-assisted and automated software development has created increased risk to the ...

Organisations face significant security risks in the era of "vibe coding" and AI-generated software. A recent benchmark ...

Many Australian organisations believe their identity security is robust, but much of it relies on outdated, static ...
No results found.

Global enterprises are under mounting pressure to rethink how and where they manage data. Cross-border transfers, cloud ...

Introduction
Security and governance are no longer back-office concerns, and in Australia, the stakes have never been ...
As cyber threats evolve and quantum computing looms, organizations are shifting from breach prevention to ...
No results found.

The next cyberattack could be human, or a human engineering an AI from the outside, or an AI engineered from the inside. ...

Cyber incidents start quietly, which looks like a compromised credential, a malicious attachment, an employee doing what ...
I was researching cyberattacks, and a common theme popped out. “We had an unprecedented cyberattack… and we shut down our ...
No results found.

Most Australian enterprises believe they have identity security under control. Frameworks are in place, policies are ...

Introduction
In Australia, the intensity of our airport and aviation security is strangely famous worldwide. It even has ...

Access control has long been treated as a function of facilities teams, focused on unlocking and locking doors. As digital ...
No results found.

Buying AI tools is easy. Building the infrastructure to support them is not as easy.
According to John Hines, Senior ...

Many organisations still prioritise operational speed over security hardening, particularly when systems are ‘good enough’ ...

The next cyberattack could be human, or a human engineering an AI from the outside, or an AI engineered from the inside. ...
No results found.

Manufacturing has always depended on stable operations. That used to mean keeping machines running, maintaining quality, ...

Most people thought that cybersecurity is all about data breaches, suspicious links, or adversaries trying to get access ...
As global security threats evolve, so must the approach to access control. According to the 2025 Trends in Access ...
No results found.

There is enormous attention on generative AI (GenAI) and its potential to change software development. While the full ...

Introduction
With the end of the financial year (EOFY) fast approaching, it’s more important now than ever for businesses ...

As insurers impose stricter limitations, manufacturers must revise their risk management strategies and implement ...
No results found.