The Voice of Cyber®
News & Thoughts
Stay up-to-date on the news with press releases from some of the biggest organisations and deep-dive articles from leaders within the industry.
Deep Dive Articles

Australian Public: How to add 2FA
Two-Factor Authentication (2FA) is a necessity to ensure your daily security, no matter who you are. It can protect your social media accounts, banking accounts, email, or just about any other online service from being hacked. “How?” you ask. Well, let’s take a closer look at how it works and how to get it working fast. To keep your online identity as ...

Privacy Has a Business Model Problem
Business growth should not come at the expense of customer privacy. Unfortunately, that’s not a belief that everybody holds, and the result is an environment in which data privacy breaches are increasing in regularity and severity. Whether it’s Facebook, Cambridge Analytica and The US Elections, or any of the nearly 1,000 incidents received by Office ...
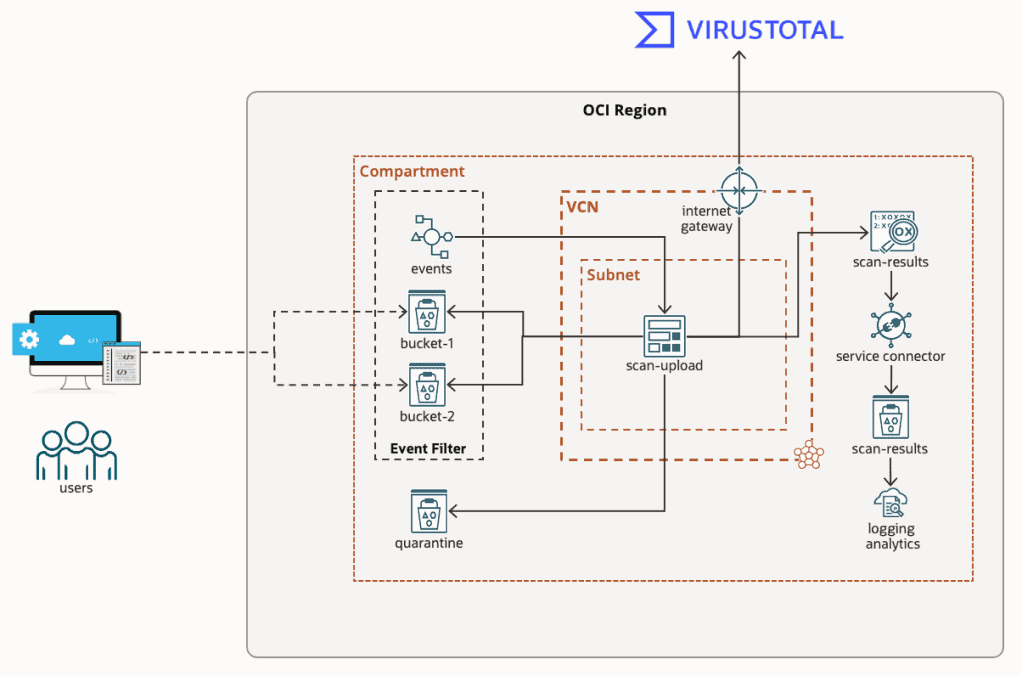
Virus & Malware Scanning Object Storage in OCI
If you’re like me, then working in IT means you also assume Tech Support duties for friends, family, and those distant relatives that only seem to call when they’ve got a problem.
I just clicked on this link, and my computer is doing something weird. I think my PC has a virus, what do I do?
When it’s just a single computer, the answer is simple, ...
Tenable Research Reveals “Do-It-Yourself” Ransomware Kits Have Created Thriving Cottage Industry of Cybercrime
The self-sustaining ransomware industry earned $692m from collective attacks in 2020 The shift to the subscription economy has created a new norm in the as-a-service world. And it’s not just Netflix and Spotify that have adopted this business model. New research from Tenable®, the Cyber Exposure company, found that one of the main reasons ransomware ...
Tenable Research Reveals “Do-It-Yourself” Ransomware Kits Have Created Thriving Cottage Industry of Cybercrime
The self-sustaining ransomware industry earned $692m from collective attacks in 2020 The shift to the subscription economy has created a new norm in the as-a-service world. And it’s not just Netflix and Spotify that have adopted this business model. New research from Tenable®, the Cyber Exposure company, found that one of the main reasons ransomware ...
Darktrace – Media Roundtable | Event Report
I was recently invited to a Roundtable Media Event held by Darktrace to unpack the new era of cyber security threats. Held on Thursday 16th June, it was led by Tony Jarvis, Director of Enterprise Security and Dave Palmer, Chief Product Officer.
The following is a synopsis of the event and a deeper dive into what was covered.
Most Significant ...
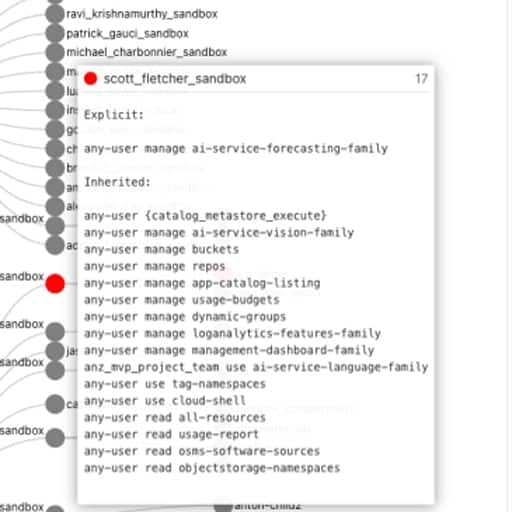
OCI User Access Review Made Easy
I’m sure we can all agree, adopting a cloud strategy is awesome. The opportunities and benefits it affords are many. However cloud governance is an ongoing problem that plagues security, compliance, and management teams, which cloud vendors like Oracle are continually trying to solve.
If you’re reading this, you’ve probably been asked, or heard at ...
Media Alert: Scammers Hack Twitter Accounts to Steal Popular NFTs and Digital Currencies
According to recent research, published by Tenable’s Staff Research Engineer, Satnam Narang, scammers have once again dug deep into their bag of tricks to capitalise on the fervour in non-fungible tokens (NFT) and cryptocurrencies.
Many are hijacking verified and unverified accounts on Twitter to impersonate popular NFT projects including Bored Ape ...
No results found.
In The News
Cohesity and 11:11 Systems Launch Clean Room Recovery Service to Bolster Cyber Resilience
Industry-First Cloud-Based Solution, now Generally Available, Enables Rapid Cyber Incident Response, Mass Restoration, and Confident Recovery Through an On-Demand Service Model
SentinelOne Honour Innovative Australian Partners at 2025 APJ PartnerOne Summit Awards
Sydney, June 11, 2025 – SentinelOne® (NYSE: S), a global leader in AI-powered security, has announced the Australian winners of its 2025 APJ PartnerOne Awards, recognising their outstanding contributions to innovation in security solutions among the company’s partners in the Asia Pacific and Japan region.
The awards were presented during the company’s ...
Pax8 Unveils Major Marketplace Enhancements with Integrations Hub and Public Storefronts
SYDNEY, NSW (June 11, 2025) – Pax8, the leading cloud commerce Marketplace, today announced significant enhancements to its Marketplace, introducing powerful new capabilities designed to streamline operations for managed service providers (MSPs). These advancements – the Integrations Hub and Public Storefronts - further solidify Pax8's commitment to ...
Datadog Scales AI Security for End-to-End Risk Protection
Launch of Code Security and new security capabilities strengthen posture across the AI stack, from data and AI models to applications
Pax8 Enhances Partner Engagement Initiatives with Renewed Partner Experience Team
SYDNEY, NSW (June 11, 2025) – Pax8, the leading cloud commerce Marketplace, today announced its elevated commitment to partner engagement and partner listening with a series of new and enhanced programs driven by Pax8’s partner experience team that will now be led by Rob Rae, Pax8 Corporate Vice President of Community and Partner Experience. Rob Rae ...
Datadog Unveils Advanced LLM Observability Tools to Enhance AI Agent Performance and Monitoring
AI Agent Monitoring, LLM Experiments and AI Agents Console help organisations measure and justify agentic AI investments
A/NZ AI Anxiety Remains Despite Broad Recognition of Value: ManageEngine Study
Nearly two-thirds of respondents believe organisations cannot afford to ignore AI despite 57 per cent expressing some anxiety
Barracuda Researchers Reveal Two Emerging Email Threats Including Revamped ‘EvilProxy’ Phishing Kit
Email Threat Radar – June 2025, During May, Barracuda threat analysts identified several notable email-based threats targeting organisations around the world and designed to evade detection and boost the chances of success, including:
The EvilProxy phishing kit resurfacing with new attacks and tactics, such as:
Spoofing the Upwork employment ...
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
- 153
- 154
- 155
- 156
- 157
- 158
- 159
- 160
- 161
- 162
- 163
- 164
- 165
- 166
- 167
- 168
- 169
- 170
- 171
- 172
- 173
- 174
- 175
- 176
- 177
- 178
- 179
- 180
- 181
- 182
- 183
- 184
- 185
- 186
- 187
- 188
- 189
- 190
- 191
- 192
- 193
- 194
- 195
- 196
- 197
- 198
- 199
- 200
- 201
- 202
- 203
- 204
- 205
- 206
- 207
- 208
- 209
- 210
- 211
- 212
- 213
- 214
- 215
- 216
- 217
- 218
- 219
- 220
- 221
- 222
- 223
- 224
- 225
- 226
- 227
- 228
- 229
- 230
- 231
- 232
- 233
- 234
- 235
- 236
- 237
- 238
- 239
- 240
- 241
- 242
- 243
- 244
- 245
- 246
- 247
- 248
- 249
- 250
- 251
- 252
- 253
- 254
- 255
- 256
- 257
- 258
- 259
- 260
- 261
- 262
- 263
- 264
- 265
- 266
- 267
- 268
- 269
- 270
- 271
- 272
- 273
- 274
- 275
- 276
- 277
- 278
- 279
- 280
- 281
- 282
- 283
- 284
- 285
- 286
- 287
- 288
- 289
- 290
- 291
- 292
- 293
- 294
- 295
- 296
- 297
- 298
- 299
- 300
- 301
- 302
- 303
- 304
- 305
- 306
- 307
- 308
- 309
- 310
- 311
- 312
- 313
- 314
- 315
- 316
- 317
- 318
- 319
- 320
- 321
- 322
- 323
- 324
- 325
- 326
- 327
- 328
- 329
- 330
- 331
- 332
- 333
- 334
- 335
- 336
No results found.
What We Do
KBI.Media is The Voice of Cyber.
We broadcast some of the most important and informative cyber content from some of the largest organisations, governments, and promising start-ups from around the world.
We're also responsible for creating a lot of it..
