The Voice of Cyber®
News & Thoughts
Stay up-to-date on the news with press releases from some of the biggest organisations and deep-dive articles from leaders within the industry.
Deep Dive Articles

Battling Cyber Scams: Traditional Algorithms Won’t Cut IT
Australians have experienced a surge in scams, with losses amounting to a staggering $3.1 billion in the past year alone. From a cybersecurity perspective, traditional anti-fraud analytics won’t stem the rising tide of scams. FICO's Vaile Mexted shares five key considerations for the finance sector as it faces an urgent imperative to fortify defences ...

Building Bridges: Developing Cybersecurity Skills and Elevating Talent
The cybersecurity sector is at a crossroads, grappling with what can only be described as an existential crisis. The gap in cybersecurity skills has grown to alarming proportions with Australia boasting a shortage of 25,000 to 30,000 cybersecurity professionals in 2022.
The escalating complexity of cyber threats, showcased by the 95% increase in ...

Legal Privilege – for Cyber Incidents
A class action lawsuit has been filed against the telecommunications company Optus by former and current customers whose personal information was exposed in a data breach. The lawsuit, representing millions of customers, alleges that Optus failed to protect customer information, breached privacy and telecommunication laws, and did not take proper steps ...
2024 Cybersecurity Predictions From CyberArk
Over 2023, we’ve seen what I like to call the ‘verticalisation of cybersecurity’ taking effect, in that cybersecurity has finally taken centre stage in business discussions. cybersecurity’s impact on business is now recognised across all industries. It has become both a business concern and a disruptive force and has consequently become an integral ...
2024 Cybersecurity Predictions by Qualys
Reflecting on the past year, we've witnessed a notable transformation in how organisations perceive and prioritise their cybersecurity strategies, largely driven by evolving perspectives on its significance, impact and value it has from a business perspective, compounded by the influence of government-led legislations that emphasize compliance. ...
A Skills Shortage Should Not Define an Organisation’s Cybersecurity Posture
Australia remains in the midst of a skills shortage, with slow hiring conditions occurring across the nation. Topping the most desired positions are cybersecurity professionals, according to recruiter Hays’ Salary Guide. With the increasing significance cybersecurity has within organisations this doesn’t come as a surprise, however business leaders ...
Phishing-Resistant MFA Helps Businesses Reduce Risk and Costs in the Face of a Rapidly Changing Cyber Insurance Landscape
With the escalating rate of cyber incidents taking place, businesses are no doubt assessing cyber insurance protection. Yubico's Josh Cigna provides insights into how phishing-resistant MFA helps businesses reduce risk and costs in the face of a rapidly changing cyber insurance landscape.
Nozomi Networks Predicts Major A/NZ Critical Infrastructure Cybersecurity Uplift in 2024
Experts in Australia and New Zealand predict critical infrastructure owners will enhance operational technology security as legislative changes take shape, but skills shortages and visibility over networks remain key issues.
No results found.
In the News
Sophos Launches ITDR to Protect Against Growing Identity-Based Attacks
Today, Sophos announced the launch of Sophos Identity Threat Detection and Response (ITDR). This new solution for Sophos XDR and Sophos MDR continuously monitors customer environments for identity risks and misconfigurations and scans the dark web for compromised credentials. It enables organizations to detect and respond to identity-based attacks ...
Splunk Report Shows Observability Is a Business Catalyst for AI Adoption, Customer Experience, and Product Innovation
Cisco today announced the release of the Splunk State of Observability 2025: The Rise of a Business Catalyst report, marking its fifth annual analysis into the evolving landscape of observability. This year's research highlights the critical role observability plays in delivering business value – from elevating customer experience and boosting employee ...
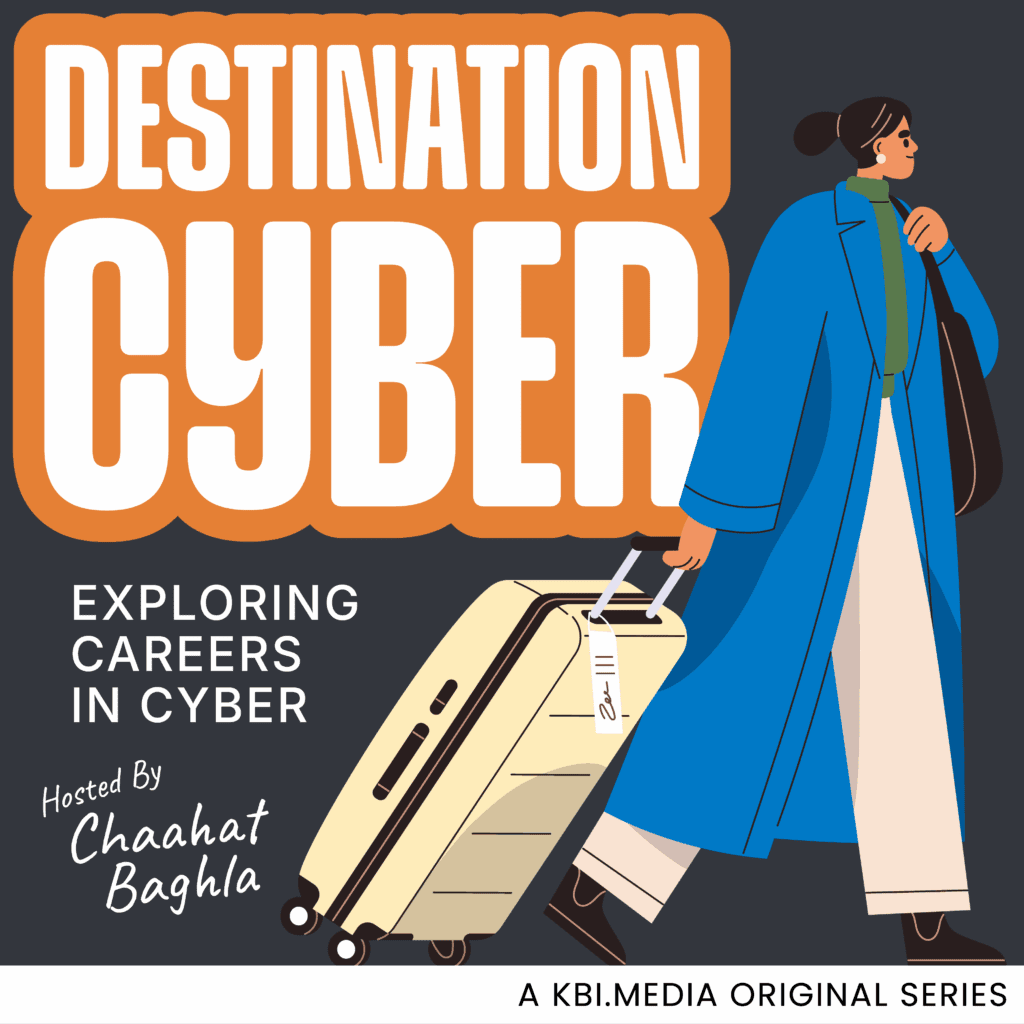
KBI.Media Announces Season Two of Destination Cyber, With New Host Chaahat Baghla
Sydney, Australia - Oct 21st - KBI.Media is proud to announce the launch of Destination Cyber: Season Two, featuring new host Chaahat Baghla, a rising cybersecurity voice and final-year student at Macquarie University, where she is completing a Bachelor of Cybersecurity.
Baghla brings a student’s perspective and professional curiosity to the platform, ...
Salty Much: Darktrace’s View on a Recent Salt Typhoon Intrusion
Salt Typhoon, a China-linked cyber espionage group, has been observed targeting global infrastructure using stealthy techniques such as DLL sideloading and zero-day exploits. Darktrace recently identified early-stage intrusion activity consistent with Salt Typhoon’s tactics, reinforcing the importance of anomaly-based detection over traditional ...
CrowdStrike 2025 APJ eCrime Landscape Report: Chinese Underground Marketplaces Drive Billions in Illicit Transactions; AI-accelerated Ransomware Surges
Chinese-speaking actors evade government restrictions and solicit criminal services through anonymized marketplaces; AI-accelerated ransomware operations signal next evolution of threats
DroneShield Strengthens Technology Leadership Team
DroneShield has announced the appointment of Angus Harris to the role of Chief Technology Officer (CTO). This appointment reflects the Company’s continued growth and organisational maturity as it scales to meet accelerating global demand across defence and government markets. Mr. Harris brings a wealth of technical and leadership experience from his ...
Quorum Cyber Named CyberSecurity Breakthrough’s Managed Security Service Provider of the Year 2025
This latest award closely follows several other accolades for Quorum Cyber this year, including being named Security MSSP of the Year in the Microsoft Security Excellence Awards 2025, winning the Cybersecurity Company of the Year award at the 2025 Scottish Cyber Awards, and being named a finalist in the Cyber Security Team of the Year category at the ...
Camelot Secure and DigiFlight Win Top Honors at Maryland’s Cybersecurity Association 2025 Cybersecurity Awards
The high-profile recognition reflects Camelot Secure’s groundbreaking work in fostering new pipelines of cybersecurity talent through its partnerships with Universities and Historically Black Colleges and Universities (HBCUs). These initiatives empower students through real-world projects, capstones, internships, and hands-on use of Camelot Secure’s ...
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
- 153
- 154
- 155
- 156
- 157
- 158
- 159
- 160
- 161
- 162
- 163
- 164
- 165
- 166
- 167
- 168
- 169
- 170
- 171
- 172
- 173
- 174
- 175
- 176
- 177
- 178
- 179
- 180
- 181
- 182
- 183
- 184
- 185
- 186
- 187
- 188
- 189
- 190
- 191
- 192
- 193
- 194
- 195
- 196
- 197
- 198
- 199
- 200
- 201
- 202
- 203
- 204
- 205
- 206
- 207
- 208
- 209
- 210
- 211
- 212
- 213
- 214
- 215
- 216
- 217
- 218
- 219
- 220
- 221
- 222
- 223
- 224
- 225
- 226
- 227
- 228
- 229
- 230
- 231
- 232
- 233
- 234
- 235
- 236
- 237
- 238
- 239
- 240
- 241
- 242
- 243
- 244
- 245
- 246
- 247
- 248
- 249
- 250
- 251
- 252
- 253
- 254
- 255
- 256
- 257
- 258
- 259
- 260
- 261
- 262
- 263
- 264
- 265
- 266
- 267
- 268
- 269
- 270
- 271
- 272
- 273
- 274
- 275
- 276
- 277
- 278
- 279
- 280
- 281
- 282
- 283
- 284
- 285
- 286
- 287
- 288
- 289
- 290
- 291
- 292
- 293
- 294
- 295
- 296
- 297
- 298
- 299
- 300
- 301
- 302
- 303
- 304
- 305
- 306
- 307
- 308
- 309
- 310
- 311
- 312
- 313
- 314
- 315
- 316
- 317
- 318
- 319
- 320
- 321
- 322
- 323
- 324
- 325
- 326
- 327
- 328
- 329
- 330
- 331
- 332
- 333
- 334
- 335
- 336
- 337
- 338
- 339
- 340
- 341
- 342
- 343
- 344
- 345
- 346
- 347
- 348
- 349
- 350
- 351
- 352
- 353
- 354
- 355
- 356
- 357
- 358
- 359
- 360
- 361
- 362
- 363
- 364
No results found.
What We Do
KBI.Media is The Voice of Cyber.
We broadcast some of the most important and informative cyber content from some of the largest organisations, governments, and promising start-ups from around the world.
We're also responsible for creating a lot of it..
