The Voice of Cyber®
News & Thoughts
Stay up-to-date on the news with press releases from some of the biggest organisations and deep-dive articles from leaders within the industry.
Deep Dive Articles

Australia’s Next Insider Threat Might Be an Algorithm
As Australian organisations race to embed AI tools across human resources, finance and operations, they may be missing a critical security fault line. While disgruntled employees or contractors gone rogue remain a concern, the next major data breach is increasingly likely to come from an algorithm that never intended malice.

Safeguarding Australia’s Most Critical Systems: Why Cybersecurity Is a Sovereignty Issue
Byline from Christopher Rule, General Manager of Defence, Security, and Resilence at GME about why cybersecurity is a sovereignty issue, on the back off ASD's recent Cyber Threat Report and ASIO Director-General Mike Burgess's speech on cyber espionage against critical infrastructure no longer being a hypothetical wartime scenario.

Exploring Security in the Context of AI
Insights From the Cisco Live! "Redefining Security in the AI Era" Panel
The rapid proliferation of Artificial Intelligence (AI) across industries has adroitly shifted the paradigm of cybersecurity. At the recent “Redefining Security in the AI Era” panel held at Cisco Live! 2025, senior leaders from Cisco, and partner organisation Logicalis, met to ...

Cybercrime to Hit $10.5 Trillion by 2025, According to Cybersecurity Ventures
According to research from Cybersecurity Ventures, cybercrime is projected to cost the world $10.5 trillion annually by 2025 ¹ and attacks, especially ransomware, are now an everyday fact of life. Last week in New York, at a recent press briefing before the official commencement of Commvault Shift, Commvault disclosed that 78% of respondents in the ...

‘We Let the Internet Down Today’ Says Co-Founder at Cloudflare
When Cloudflare goes down, the internet feels it. The recent Cloudflare outage wasn’t just ‘a blip’ - it was an unfortunate failure that took some of the world’s most heavily trafficked services offline.
Cloudflare confirmed that a configuration update triggered a failure inside its control plane, specifically within systems responsible for managing ...
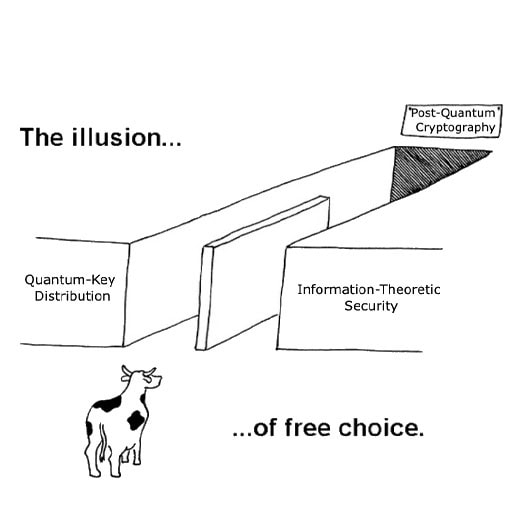
Like IT or Not, PQC Is the Key (for Now)
Every few months, another “quantum-safe” technology is marketed as the real answer, usually with the claim that post-quantum cryptography isn’t enough. PQC is too new, too slow, too fragile, too unproven. One person I spoke to even described adopting PQC as “shuffling the furniture on a sinking ship,” as if the standards effort itself is the ...
The ABCs of GRC
Introduction
In the face of increasing regulatory pressure, rising cyber threats, and growing business complexity, organisations need a structured, scalable approach to managing risk. Governance, Risk, and Compliance (GRC) frameworks have become vital for aligning information security with corporate objectives, ensuring operational resilience, and ...

The Korean Leaks – Analysing the Hybrid Geopolitical Campaign Targeting South Korean Financial Services With Qilin RaaS
When preparing data for the Bitdefender Threat Debrief | October 2025, Bitdefender noticed a significant departure from established ransomware trends. Typically, the top five most impacted countries are consistently the US, Canada, and major Western European nations. However, for this period, South Korea (KR) suddenly became the second most-targeted ...
No results found.
In the News
TrendAI™ and Anthropic Advance AI-powered Vulnerability Detection and Risk Mitigation With Claude Opus 4.7
TrendAI reinforces global threat intelligence leadership with Anthropic's Claude Opus 4.7 | Collaboration bridges gap between vulnerability discovery and real-world risk reduction
DigiCert Launches Content Trust Manager to Help Organizations Verify Digital Content Authenticity in the Age of AI
New solution enables enterprises to cryptographically prove content origin and integrity without requiring their own C2PA-compliant signing infrastructure
The Fortinet 2026 Global Threat Landscape Report Reveals a Surge in AI-Enabled Cybercrime, Contributing to a 389 per Cent Increase in Ransomware Victims Year-Over-Year
Fortinet leverages threat intelligence to disrupt global cybercrime, transforming awareness into actionable insights
Celebrities’ and Influencers’ Private Communications Exposed in Stalkerware Data Breach
Introduction
Recently cybersecurity researcher Jeremiah Fowler discovered a non-password-protected and publicly accessible database that contained 86,859 images of what looked like screenshots of a user’s device, apparently related to stalkerware targeting one specific person. It logged activity and chat conversations from Facebook, WhatsApp, ...
DigiCert Introduces New AI Trust Architecture for Securing AI Agents, Models, and Content
New capabilities bring cryptographic proof to how AI systems are secured and governed

Australia Post Taps Global AI Expertise to Supercharge Cyber Threat Detection
Australia Post is partnering with Alpha Level, a next generation AI security company, co-founded by international machine learning expert Dr. Josh Neil, to sharpen its cyber defences and speed up threat detection across its network.
Alpha Level will apply cutting-edge machine learning to help Australia Post efficiently collect, process and analyse ...
Macquarie Technology Group, Macquarie University Partner to Develop Research and Learning Pathways
Macquarie Technology Group (ASX: MAQ) and Macquarie University today announced a strategic partnership to support future collaboration across research, technology and innovation.
The agreement establishes a framework for the two organisations to collaborate in areas including cloud computing, cyber security, data centre engineering, and technology ...
xReality Group Limited Quarterly Activities Report
xReality Group Limited (ASX:XRG) (xReality) has announced its Quarterly Activities Report and Appendix 4C for the quarter ending 31st March 2026, together with an Operational Update.
Key Highlights
Cash Receipts of $5.6m (up 62% on PcP)
$17.0m YTD (up 31% on PcP)
Positive Net Operating Cashflow of $1.3m (up $1.64m on PcP)
$3.6m ...
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
- 153
- 154
- 155
- 156
- 157
- 158
- 159
- 160
- 161
- 162
- 163
- 164
- 165
- 166
- 167
- 168
- 169
- 170
- 171
- 172
- 173
- 174
- 175
- 176
- 177
- 178
- 179
- 180
- 181
- 182
- 183
- 184
- 185
- 186
- 187
- 188
- 189
- 190
- 191
- 192
- 193
- 194
- 195
- 196
- 197
- 198
- 199
- 200
- 201
- 202
- 203
- 204
- 205
- 206
- 207
- 208
- 209
- 210
- 211
- 212
- 213
- 214
- 215
- 216
- 217
- 218
- 219
- 220
- 221
- 222
- 223
- 224
- 225
- 226
- 227
- 228
- 229
- 230
- 231
- 232
- 233
- 234
- 235
- 236
- 237
- 238
- 239
- 240
- 241
- 242
- 243
- 244
- 245
- 246
- 247
- 248
- 249
- 250
- 251
- 252
- 253
- 254
- 255
- 256
- 257
- 258
- 259
- 260
- 261
- 262
- 263
- 264
- 265
- 266
- 267
- 268
- 269
- 270
- 271
- 272
- 273
- 274
- 275
- 276
- 277
- 278
- 279
- 280
- 281
- 282
- 283
- 284
- 285
- 286
- 287
- 288
- 289
- 290
- 291
- 292
- 293
- 294
- 295
- 296
- 297
- 298
- 299
- 300
- 301
- 302
- 303
- 304
- 305
- 306
- 307
- 308
- 309
- 310
- 311
- 312
- 313
- 314
- 315
- 316
- 317
- 318
- 319
- 320
- 321
- 322
- 323
- 324
- 325
- 326
- 327
- 328
- 329
- 330
- 331
- 332
- 333
- 334
- 335
- 336
- 337
- 338
- 339
- 340
- 341
- 342
- 343
- 344
- 345
- 346
- 347
- 348
- 349
- 350
- 351
- 352
- 353
- 354
- 355
- 356
- 357
- 358
- 359
- 360
- 361
- 362
- 363
- 364
No results found.
What We Do
KBI.Media is The Voice of Cyber.
We broadcast some of the most important and informative cyber content from some of the largest organisations, governments, and promising start-ups from around the world.
We're also responsible for creating a lot of it..
