The Voice of Cyber®
News & Thoughts
Stay up-to-date on the news with press releases from some of the biggest organisations and deep-dive articles from leaders within the industry.
Deep Dive Articles

‘We Let the Internet Down Today’ Says Co-Founder at Cloudflare
When Cloudflare goes down, the internet feels it. The recent Cloudflare outage wasn’t just ‘a blip’ - it was an unfortunate failure that took some of the world’s most heavily trafficked services offline.
Cloudflare confirmed that a configuration update triggered a failure inside its control plane, specifically within systems responsible for managing ...
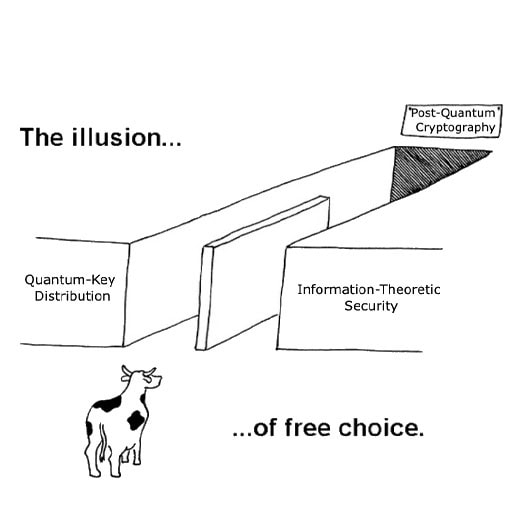
Like IT or Not, PQC Is the Key (for Now)
Every few months, another “quantum-safe” technology is marketed as the real answer, usually with the claim that post-quantum cryptography isn’t enough. PQC is too new, too slow, too fragile, too unproven. One person I spoke to even described adopting PQC as “shuffling the furniture on a sinking ship,” as if the standards effort itself is the ...
The ABCs of GRC
Introduction
In the face of increasing regulatory pressure, rising cyber threats, and growing business complexity, organisations need a structured, scalable approach to managing risk. Governance, Risk, and Compliance (GRC) frameworks have become vital for aligning information security with corporate objectives, ensuring operational resilience, and ...

The Korean Leaks – Analysing the Hybrid Geopolitical Campaign Targeting South Korean Financial Services With Qilin RaaS
When preparing data for the Bitdefender Threat Debrief | October 2025, Bitdefender noticed a significant departure from established ransomware trends. Typically, the top five most impacted countries are consistently the US, Canada, and major Western European nations. However, for this period, South Korea (KR) suddenly became the second most-targeted ...

Post Qantas Breach What Happens Now
Months after a breach hit Qantas Airways, the airline recently confirmed that stolen customer information has now been released publicly by cybercriminals. This is despite the airline’s legal efforts to prevent the stolen data from being accessed, shared, and published. Experts are now helping Qantas to establish what data has been leaked, but early ...

Oracle Is All in on AI Everything
Oracle is keeping up with the AI moment, like the rest of Silicon Valley. The database company, as we know it, is aware they need to move down the AI path to keep relevant and to keep up with customer demands. Well, truth be told, Oracle is betting big and is going all in on defining AI. Oracle’s big bet on ‘AI Native Data’ is their newest release, as ...

How the Financial Sector Is Battling New Cyber Threats
Graph databases are already proving their worth across fraud detection, compliance, and AI enablement. Their promise, however, extends further to a future where financial institutions can act not just faster, but smarter.
Turning Hesitation Into Action
Unpacking Cisco and Governance Institute’s AI Risk Report at Cisco Live! 2025
No results found.
In the News
Tenable Expands Exposure Management With Instant OT Discovery to Secure Cyber-Physical Systems
New asset discovery engine significantly accelerates AI-powered exposure management maturity
AI Emerges as the Key to Scaling MSP Operations as Growth Gets Harder
Kaseya’s 2026 State of the MSP Report finds 48% of MSPs rank AI as the number one client need, while shrinking deals and a widening talent gap make AI-driven efficiency essential to protecting margins.
Claroty Bridges Gap Between Asset Visibility and Actionable Risk Reduction With Industry-First Visibility Orchestration Capabilities
Claroty xDome’s New Visibility Orchestration Transforms Incomplete Asset Data into Prioritised Security Actions for Complex Cyber-Physical Systems Environments
WatchGuard and Halo Announce Partnership to Deliver MSP Automation From Alert to Invoice
Integration embeds WatchGuard security operations inside HaloPSA, streamlining ticketing, provisioning, and billing workflows for MSPs
Kyndryl Introduces Sovereignty Readiness Assessment and Solutioning to Support Business Continuity
New sovereignty services help organisations identify dependencies, risks and options to support continuity across complex IT environments
Commvault Targets AI Risk With New Platform Capabilities for Governance, Recovery and Control
Commvault has launched a new set of AI-driven capabilities aimed at helping organisations adopt agentic AI while maintaining control over data, governance, and cyber resilience.
Delivered through Commvault Cloud, the new offerings—Data Activate, AI Protect, and AI Studio—are designed to address one of the biggest challenges facing enterprises today: ...
Cloudflare Expands Its Agent Cloud to Power the Next Generation of Agents
As the way software is built fundamentally changes, Cloudflare introduces the infrastructure to power millions of autonomous, long-running agents
Only 5% of Organisations Have Full Trust in Their Cybersecurity Vendors
Sophos today released findings from a global, vendor-agnostic study (based on responses from 5,000 organisations across 17 countries), examining one of cybersecurity’s most urgent and overlooked necessities: trust.
The Cybersecurity Trust Reality 2026 report is one of the most comprehensive studies of trust in cybersecurity and the impact on ...
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
- 153
- 154
- 155
- 156
- 157
- 158
- 159
- 160
- 161
- 162
- 163
- 164
- 165
- 166
- 167
- 168
- 169
- 170
- 171
- 172
- 173
- 174
- 175
- 176
- 177
- 178
- 179
- 180
- 181
- 182
- 183
- 184
- 185
- 186
- 187
- 188
- 189
- 190
- 191
- 192
- 193
- 194
- 195
- 196
- 197
- 198
- 199
- 200
- 201
- 202
- 203
- 204
- 205
- 206
- 207
- 208
- 209
- 210
- 211
- 212
- 213
- 214
- 215
- 216
- 217
- 218
- 219
- 220
- 221
- 222
- 223
- 224
- 225
- 226
- 227
- 228
- 229
- 230
- 231
- 232
- 233
- 234
- 235
- 236
- 237
- 238
- 239
- 240
- 241
- 242
- 243
- 244
- 245
- 246
- 247
- 248
- 249
- 250
- 251
- 252
- 253
- 254
- 255
- 256
- 257
- 258
- 259
- 260
- 261
- 262
- 263
- 264
- 265
- 266
- 267
- 268
- 269
- 270
- 271
- 272
- 273
- 274
- 275
- 276
- 277
- 278
- 279
- 280
- 281
- 282
- 283
- 284
- 285
- 286
- 287
- 288
- 289
- 290
- 291
- 292
- 293
- 294
- 295
- 296
- 297
- 298
- 299
- 300
- 301
- 302
- 303
- 304
- 305
- 306
- 307
- 308
- 309
- 310
- 311
- 312
- 313
- 314
- 315
- 316
- 317
- 318
- 319
- 320
- 321
- 322
- 323
- 324
- 325
- 326
- 327
- 328
- 329
- 330
- 331
- 332
- 333
- 334
- 335
- 336
- 337
- 338
- 339
- 340
- 341
- 342
- 343
- 344
- 345
- 346
- 347
- 348
- 349
- 350
- 351
- 352
- 353
- 354
- 355
- 356
No results found.
What We Do
KBI.Media is The Voice of Cyber.
We broadcast some of the most important and informative cyber content from some of the largest organisations, governments, and promising start-ups from around the world.
We're also responsible for creating a lot of it..
