The Voice of Cyber®
News & Thoughts
Stay up-to-date on the news with press releases from some of the biggest organisations and deep-dive articles from leaders within the industry.
Deep Dive Articles
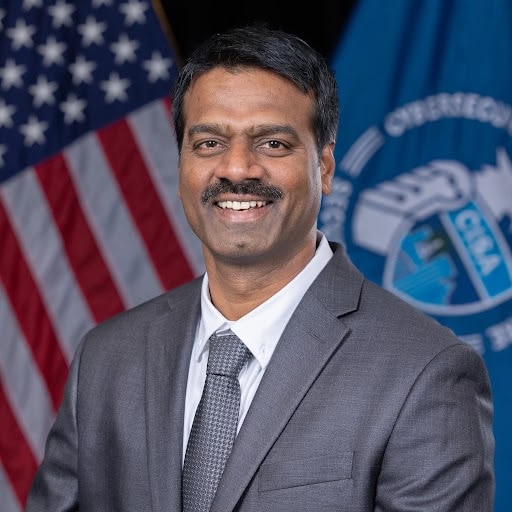
Cybersecurity Chief’s AI Slip Sparks Federal Security Review
The acting director of Cybersecurity and Infrastructure Security Agency (CISA), Madhu Gottumukkala, is facing industry scrutiny after accidentally uploading sensitive government documents into a public version of ChatGPT, according to reports online.
The documents were luckily not classified, but they were marked ‘For Official Use Only’, which is for ...

Why “IT Won’t Happen Here” Is a Dangerous Bet
Cyber incidents start quietly, which looks like a compromised credential, a malicious attachment, an employee doing what they’ve always done. The damage only becomes visible once systems stall, operations freeze, and executives ask the same question they always ask at the eleventh hour, ‘How did this get so far?’
Rajesh Khazanchi, CEO and Co-Founder ...

The Transformative Role of AI in Cybersecurity
The integration of AI and cybersecurity is reshaping the digital landscape, with three key trends emerging: the rise of AI-powered security threats, the transformation of data governance through AI, and the elevation of cybersecurity as a C-suite priority. Cybercriminals are leveraging AI for sophisticated attacks, necessitating adaptive, AI-driven ...
Email Threat Radar – January 2026
From QR code deception to callback phishing and more: An overview of emerging email threats and attack trends

When Digital Names Collide, Business Risk Follows
In an era where trust is increasingly mediated by systems rather than people, ensuring that every digital identity maps cleanly to a real one is no longer optional. It is a prerequisite for doing business safely.

Service to Our Nation Should Be the Focus According to Former NSA Deputy Director
America doesn’t have a technology problem. The biggest tech companies and CEO’s are birthed out of the United States. But, it may have a purpose problem.
With more than three decades spent inside the National Security Agency (NSA), as the former Deputy Director, George Barnes (currently Cyber Practice President and Partner at Red Cell Partners) ...

Do You Use Free Wi-Fi in Public Places?
In today's modern life, we find ourselves highly dependent on the connected world. Think about it, almost everything we do or need in some form requires being connected via a website, app or computer platform. We carry most of us smartphones which are smarter than the computer systems that enabled man to land on the moon.
Seriously, just think ...

AI Broke Cybersecurity and Corporate Leadership Still Hasn’t Noticed
Code is now being written and shipped faster than most security programs were ever built to withstand. Developers are moving at speed. Product teams are pushing releases earlier. And companies are racing to stay competitive often without fully grasping the risks they’ve just signed up for.Sonali Chaudhuri, Founder of MySmartOps commented,“...Exposing ...
No results found.
In the News
XRG Completes $5.6M US Department of Defense Project; Commercialises Technology with Launch of MR-1
xReality Group Limited (XRG) is pleased to announce that Operator XR, its defence and law-enforcement simulation subsidiary, has successfully completed all milestones of the 20-month, AU$5.6 million subcontract awarded by the United States Department of Defense (DoD), delivered as part of Team Endurance Group.
The US DoD subcontract, first announced ...
Infoblox and GoDaddy Support Open Standards for AI Agent Discovery, Identity and Verification
DNS infrastructure leaders back complementary, DNS-based approaches to help add transparency to AI agents across the open web
Boomi Joins Forces with Gong to Power Revenue AI Within Boomi Agentstudio
Gong's revenue AI is now natively available in the Boomi Enterprise Platform
Bitdefender Uncovers China-Linked APT Expanding Into Energy Sector, Exposing Global Infrastructure Risks
Bitdefender has uncovered a sophisticated cyber-espionage campaign linked to the China-aligned threat group FamousSparrow, marking a significant escalation into the global energy sector and exposing critical infrastructure risks at a time of heightened geopolitical instability.
The research details a multi-wave intrusion targeting an Azerbaijani oil ...
ESET Uncovers CallPhantom Scam on Google Play: Fake Logs for Real Money
A new Android scam, CallPhantom, falsely claims to provide access to call logs, SMS records, and WhatsApp call history for any phone number in exchange for payment. We identified and reported 28 separate CallPhantom apps on Google Play, cumulatively downloaded more than 7.3 million times. 53.7% of all CallPhantom detections worldwide were found in ...
Boomi and Couchbase Partner to Power Enterprise AI Agents with Trusted Recollection, Connectivity, and Governance
AI data activation company Boomi and operational AI data platform Couchbase, Inc. today announced a partnership through which the two companies are collaborating closely to accelerate AI pilots to production. The companies will co-engineer solutions that give customers a production-ready foundation for agentic AI, combining Boomi's connectivity, ...
EXL Unveils New Agentic AI Solutions to Accelerate Enterprise Transformation Across the Full AI Value Chain
Expanded portfolio integrates agent development, governance, decision intelligence and domain workflows to help enterprises scale AI responsibly and deliver measurable business outcomes
Semperis Publishes Study on AI’s Effect on the Attack Surface of Identity Systems
Study reveals Australian organisations are granting AI agents access to essential systems faster than safety measures are implemented. Without comprehensive security for identity systems, hackers can speed attempts to compromise Active Directory, EntraID or Okta
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
- 153
- 154
- 155
- 156
- 157
- 158
- 159
- 160
- 161
- 162
- 163
- 164
- 165
- 166
- 167
- 168
- 169
- 170
- 171
- 172
- 173
- 174
- 175
- 176
- 177
- 178
- 179
- 180
- 181
- 182
- 183
- 184
- 185
- 186
- 187
- 188
- 189
- 190
- 191
- 192
- 193
- 194
- 195
- 196
- 197
- 198
- 199
- 200
- 201
- 202
- 203
- 204
- 205
- 206
- 207
- 208
- 209
- 210
- 211
- 212
- 213
- 214
- 215
- 216
- 217
- 218
- 219
- 220
- 221
- 222
- 223
- 224
- 225
- 226
- 227
- 228
- 229
- 230
- 231
- 232
- 233
- 234
- 235
- 236
- 237
- 238
- 239
- 240
- 241
- 242
- 243
- 244
- 245
- 246
- 247
- 248
- 249
- 250
- 251
- 252
- 253
- 254
- 255
- 256
- 257
- 258
- 259
- 260
- 261
- 262
- 263
- 264
- 265
- 266
- 267
- 268
- 269
- 270
- 271
- 272
- 273
- 274
- 275
- 276
- 277
- 278
- 279
- 280
- 281
- 282
- 283
- 284
- 285
- 286
- 287
- 288
- 289
- 290
- 291
- 292
- 293
- 294
- 295
- 296
- 297
- 298
- 299
- 300
- 301
- 302
- 303
- 304
- 305
- 306
- 307
- 308
- 309
- 310
- 311
- 312
- 313
- 314
- 315
- 316
- 317
- 318
- 319
- 320
- 321
- 322
- 323
- 324
- 325
- 326
- 327
- 328
- 329
- 330
- 331
- 332
- 333
- 334
- 335
- 336
- 337
- 338
- 339
- 340
- 341
- 342
- 343
- 344
- 345
- 346
- 347
- 348
- 349
- 350
- 351
- 352
- 353
- 354
- 355
- 356
- 357
- 358
- 359
- 360
- 361
- 362
- 363
- 364
No results found.
What We Do
KBI.Media is The Voice of Cyber.
We broadcast some of the most important and informative cyber content from some of the largest organisations, governments, and promising start-ups from around the world.
We're also responsible for creating a lot of it..
