The Voice of Cyber®
News & Thoughts
Stay up-to-date on the news with press releases from some of the biggest organisations and deep-dive articles from leaders within the industry.
Deep Dive Articles

What I’ve Learnt as an Entrepreneur
A few things I’ve learnt over the years of being an Entrepreneur. This changes for me all the time, our challenges become easier to tackle and what scares us varies. Ultimately, you learn so much, and I wanted to share what I’ve learnt so far.

What I’ve Learnt as an Entrepreneur
A few things I’ve learnt over the years of being an Entrepreneur. This changes for me all the time, our challenges become easier to tackle and what scares us varies. Ultimately, you learn so much, and I wanted to share what I’ve learnt so far.

Australian Public: How to Add 2FA
Two-Factor Authentication (2FA) is a necessity to ensure your daily security, no matter who you are. It can protect your social media accounts, banking accounts, email, or just about any other online service from being hacked. “How?” you ask. Well, let’s take a closer look at how it works and how to get it working fast. To keep your online identity as ...

Privacy Has a Business Model Problem
Business growth should not come at the expense of customer privacy. Unfortunately, that’s not a belief that everybody holds, and the result is an environment in which data privacy breaches are increasing in regularity and severity. Whether it’s Facebook, Cambridge Analytica and The US Elections, or any of the nearly 1,000 incidents received by Office ...
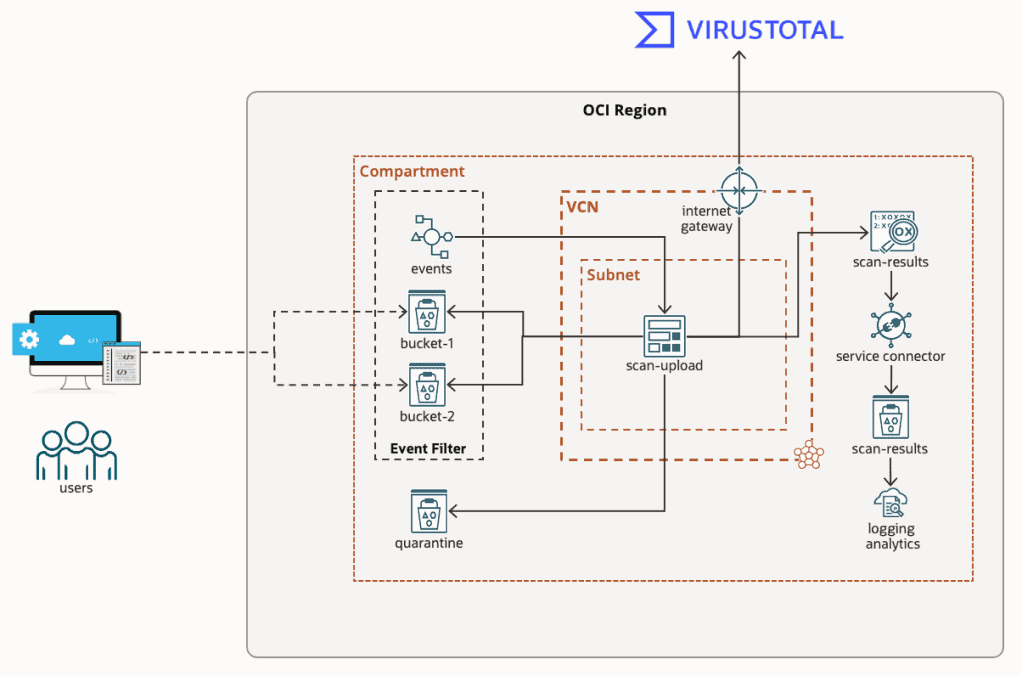
Virus & Malware Scanning Object Storage in OCI
If you’re like me, then working in IT means you also assume Tech Support duties for friends, family, and those distant relatives that only seem to call when they’ve got a problem.
I just clicked on this link, and my computer is doing something weird. I think my PC has a virus, what do I do?
When it’s just a single computer, the answer is simple, ...
Tenable Research Reveals “Do-It-Yourself” Ransomware Kits Have Created Thriving Cottage Industry of Cybercrime
The self-sustaining ransomware industry earned $692m from collective attacks in 2020 The shift to the subscription economy has created a new norm in the as-a-service world. And it’s not just Netflix and Spotify that have adopted this business model. New research from Tenable®, the Cyber Exposure company, found that one of the main reasons ransomware ...
Tenable Research Reveals “Do-It-Yourself” Ransomware Kits Have Created Thriving Cottage Industry of Cybercrime
The self-sustaining ransomware industry earned $692m from collective attacks in 2020 The shift to the subscription economy has created a new norm in the as-a-service world. And it’s not just Netflix and Spotify that have adopted this business model. New research from Tenable®, the Cyber Exposure company, found that one of the main reasons ransomware ...
Darktrace – Media Roundtable | Event Report
I was recently invited to a Roundtable Media Event held by Darktrace to unpack the new era of cyber security threats. Held on Thursday 16th June, it was led by Tony Jarvis, Director of Enterprise Security and Dave Palmer, Chief Product Officer.
The following is a synopsis of the event and a deeper dive into what was covered.
Most Significant ...
No results found.
In the News
Ransomware Attacks Surge in Australia: One in Three Hit Multiple Times – New Report
One in Three Australian Ransomware Victims Hit Multiple Times as Security Gaps Persist.
New International Research Shows Ransomware Thrives in Complex and Fragmented IT Security Environments.
F5 and Equinix Expand Partnership to Accelerate AI-Ready Infrastructure for Secure Global Application Delivery
New joint capabilities help enterprises deploy and secure distributed AI workloads and modern apps—without physical infrastructure overhead
Tenable Expands Exposure Management Platform to Secure Enterprise AI
Tenable AI Exposure gives organisations unprecedented visibility into and control over the use of widely adopted generative AI tools like ChatGPT Enterprise and Microsoft Copilot
KnowBe4 Deploys Additional Agentic Capabilities to Bolster Customers’ AI Defences
Sydney, Australia, 7 August 2025 –KnowBe4, the world-renowned cybersecurity platform that comprehensively addresses human risk management (HRM), is proud to highlight the success of its customers in achieving remarkable transformations in their HRM programs. By leveraging KnowBe4’s HRM+ platform and advanced AI-driven products including AIDA ...
CrowdStrike Launches New Services to Secure AI Systems and Operationalize AI in the SOC
AI Systems Security Assessment and AI for SecOps Readiness expand CrowdStrike’s industry-leading AI Security Services portfolio, helping organizations reduce risk and stop breaches in the AI era
CrowdStrike Signal Delivers the Next Evolution of AI-Powered Threat Detection
Now GA, new self-learning detection engines surface threats undetectable for others – connecting subtle activity into prioritized leads to accelerate investigation, hunting, and response
Securing Australia’s Critical Systems: CyberArk Completes IRAP Assessment at “Protected” Information Classification Level
CyberArk (NASDAQ: CYBR), the global leader in identity security, today announced that it has completed Australia’s InfoSec Registered Assessors Program (IRAP) assessment at the “Protected” information classification level. Public sector organisations in Australia looking for the highest national standards for safeguarding critical assets can rely on ...
Delinea Unveils Delinea Iris AI to Make Identity Security Simpler, Stronger, and Smarter
Powerful AI engine embedded natively into the Delinea Platform fuels new, innovative capabilities that deliver real-time visibility, enhanced productivity, and greater control
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
- 153
- 154
- 155
- 156
- 157
- 158
- 159
- 160
- 161
- 162
- 163
- 164
- 165
- 166
- 167
- 168
- 169
- 170
- 171
- 172
- 173
- 174
- 175
- 176
- 177
- 178
- 179
- 180
- 181
- 182
- 183
- 184
- 185
- 186
- 187
- 188
- 189
- 190
- 191
- 192
- 193
- 194
- 195
- 196
- 197
- 198
- 199
- 200
- 201
- 202
- 203
- 204
- 205
- 206
- 207
- 208
- 209
- 210
- 211
- 212
- 213
- 214
- 215
- 216
- 217
- 218
- 219
- 220
- 221
- 222
- 223
- 224
- 225
- 226
- 227
- 228
- 229
- 230
- 231
- 232
- 233
- 234
- 235
- 236
- 237
- 238
- 239
- 240
- 241
- 242
- 243
- 244
- 245
- 246
- 247
- 248
- 249
- 250
- 251
- 252
- 253
- 254
- 255
- 256
- 257
- 258
- 259
- 260
- 261
- 262
- 263
- 264
- 265
- 266
- 267
- 268
- 269
- 270
- 271
- 272
- 273
- 274
- 275
- 276
- 277
- 278
- 279
- 280
- 281
- 282
- 283
- 284
- 285
- 286
- 287
- 288
- 289
- 290
- 291
- 292
- 293
- 294
- 295
- 296
- 297
- 298
- 299
- 300
- 301
- 302
- 303
- 304
- 305
- 306
- 307
- 308
- 309
- 310
- 311
- 312
- 313
- 314
- 315
- 316
- 317
- 318
- 319
- 320
- 321
- 322
- 323
- 324
- 325
- 326
- 327
- 328
- 329
- 330
- 331
- 332
- 333
- 334
- 335
- 336
- 337
- 338
- 339
- 340
- 341
- 342
- 343
- 344
- 345
- 346
- 347
- 348
- 349
- 350
- 351
- 352
- 353
- 354
- 355
- 356
- 357
- 358
- 359
- 360
- 361
- 362
- 363
- 364
No results found.
What We Do
KBI.Media is The Voice of Cyber.
We broadcast some of the most important and informative cyber content from some of the largest organisations, governments, and promising start-ups from around the world.
We're also responsible for creating a lot of it..
