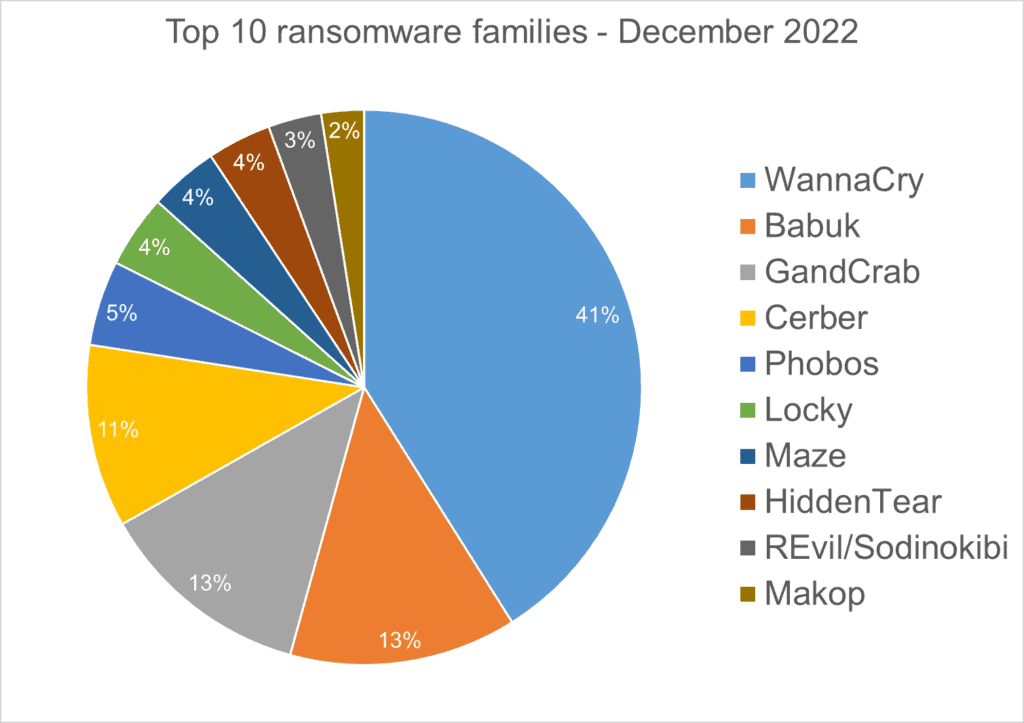
Spear phishing attacks are often used as an initial attack vector and ransomware infection is often the final stage of the kill chain. For this report, we analysed malware detections collected in December 2022 from our static anti-malware engines. Note: we only count total cases, not how monetarily significant the impact of infection is. Opportunistic adversaries and some Ransomware-as-a-Service (RaaS) groups represent a higher percentage compared to groups that are more selective about their targets, since they prefer volume over higher value.
When looking at this data, remember these are ransomware detections, not infections.
Top 10 Ransomware Families (H3)
We analysed malware detections from December 1 to December 31. In total, we identified 207 ransomware families. The number of detected ransomware families can vary each month, depending on the current ransomware campaigns in different countries.
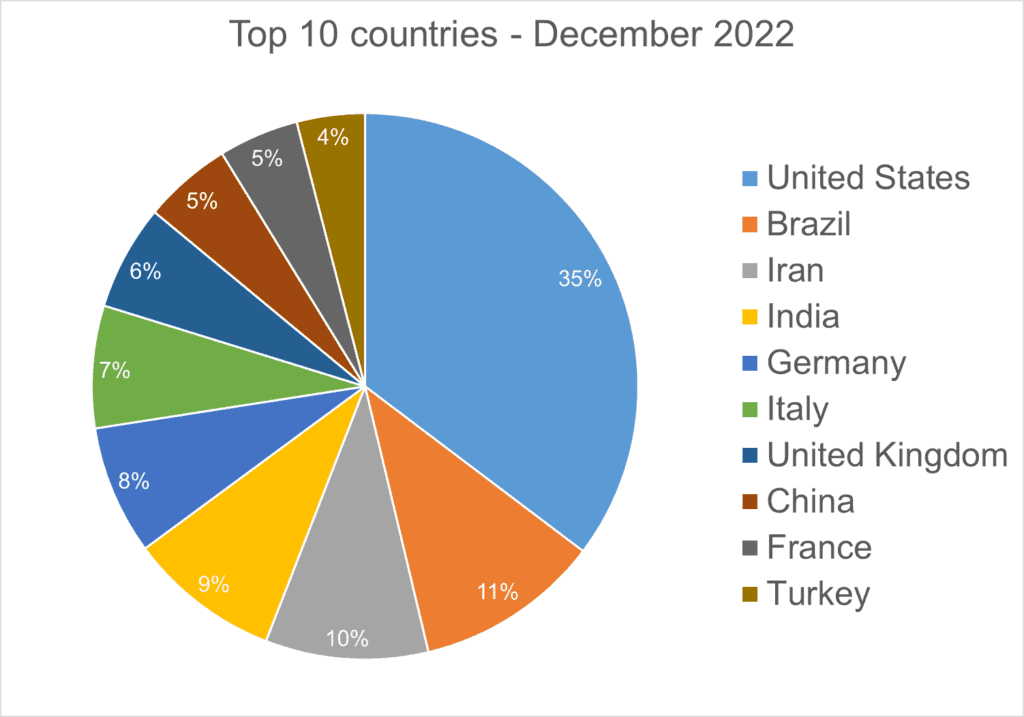
Top 10 Countries (H3)
In total, we detected ransomware from 147 countries in our dataset this month. Ransomware continues to be a threat that touches almost the entire world. Below is a list of the top 10 countries most impacted by ransomware. Many ransomware attacks continue to be opportunistic, and the size of population is correlated to the number of detections.
Android Trojans (H2)
Below are the top 10 trojans targeting Android we have seen in our telemetry during December 2023.
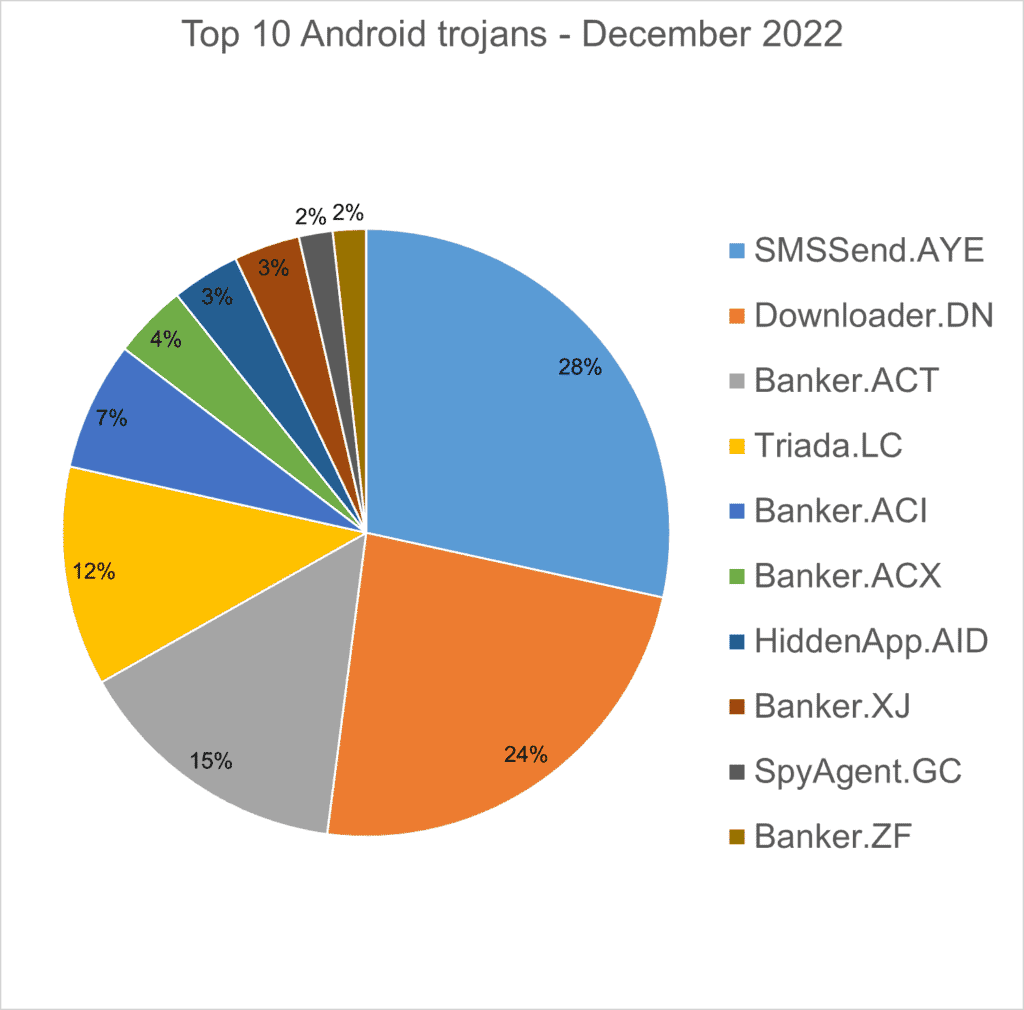
SMSSend.AYE – Malware that tries to register as the default SMS application on the first run by requesting the consent of the user. If successful, it collects the user’s incoming and outgoing messages and forwards them to a Command & Control (C&C) server.
Downloader.DN – Repacked applications taken from Google App Store and bundled with aggressive adware. Some adware downloads other malware variants.
Banker.ACT, ACI – Polymorphic applications that impersonate legit apps (Google, Facebook, Sagawa Express …). Once installed, it locates banking applications on the device and tries downloading a trojanised version from the C&C server.
Triada.LC – Malware that gathers sensitive information about a device (Device IDs, Subscriber IDs, MAC addresses) and sends them to a malicious C&C server. The C&C server responds by sending back a link to a payload that the malware downloads and executes.
Banker.ACX – Applications that impersonate Korean banking applications to record audio and video, collect sensitive information (SMS messages, contacts, GPS location…) and upload it to a C&C server.
HiddenApp.AID – Aggressive adware that impersonates AdBlock applications. When running for the first time, it asks permission to display on top of other apps. With this permission, the application can hide from the launcher.
Banker.XJ – Applications that drop and install encrypted modules. This trojan grants device admin privileges, and gains access to manage phone calls and text messages. After deploying, it maintains a connection with the C&C server to receive command and upload sensitive information.
SpyAgent.GC –Applications that exfiltrate sensitive data like SMS messages, call logs, contacts, or GPS location.
Banker.ZF – Applications that disguise themselves as banking apps and can imitate conversation with customer support. When the malware runs for the first time, it asks for permissions to access contacts, microphone, geolocation, and camera. Once the permissions are granted, the malware can receive commands from the C&C server to exfiltrate sensitive data from the phone.
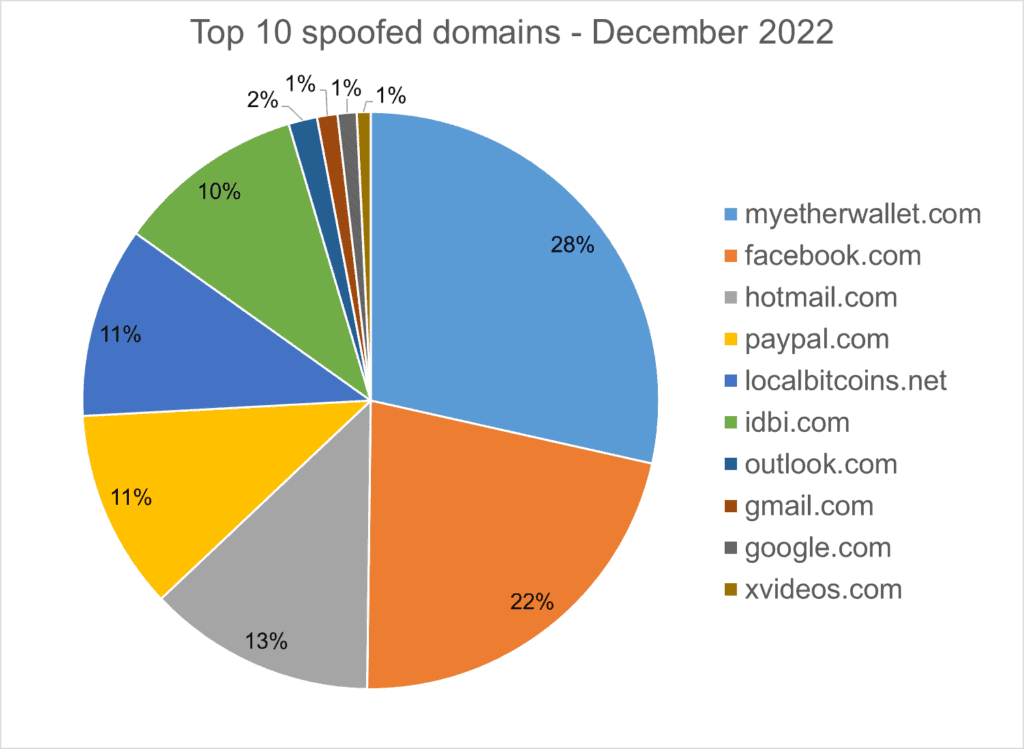
Homograph Phishing Report (H2)
Homograph attacks work to abuse international domain names (IDN). Threat actors create international domain names that spoof a target domain name. When we talk about “target” of IDN homograph phishing attacks, we refer to the domain that threat actors are trying to impersonate. You can read more about this type of attack in one of our previous reports.
Below is the list of the top 10 most common targets for phishing sites.