Two US nationals have been sentenced years behind bars after federal prosecutors say they helped fuel a sophisticated North Korean scheme that infiltrated American companies, stole identities and funnelled millions to a hostile regime.
The United States Department of Justice announced that Kejia Wang, 42, and Zhenxing Wang, 39, were sentenced for their roles in a multi year operation that enabled North Korean IT workers to pose as US-based employees and secure remote jobs across more than 100 American companies.
Authorities say the scheme generated over $5 million in illicit revenue for the Democratic People’s Republic of Korea (DPRK), raising serious national security concerns over how easily foreign adversaries can exploit remote work environments.
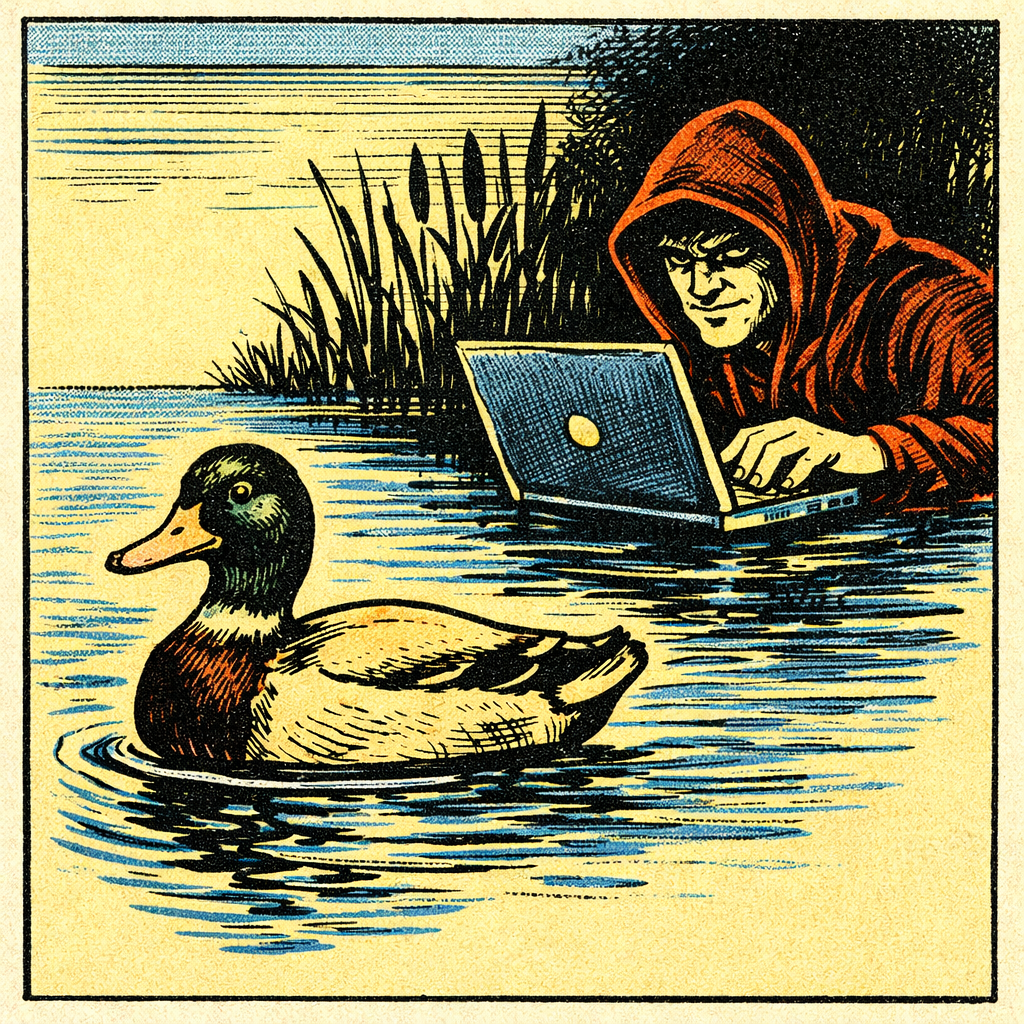
At the centre of the operation were so called ‘laptop farms’ across physical locations in the United States where company issued devices were hosted to create the illusion that workers were operating domestically, but were in fact not.
Prosecutors say those machines were remotely accessed by North Korean operatives overseas, allowing them to bypass sanctions and gain employment under stolen American identities, which is starting to become a very common occurence.
The scheme relied on the identities of at least 80 US citizens, with the fraudulent workers embedding themselves into corporate environments and in some cases, including major enterprises and sensitive sectors.
Kejia Wang was sentenced to a whopping 108 months (9 years) in prison after pleading guilty to conspiracy charges that included wire fraud, money laundering, and identity theft. Zhenxing Wang received a lesser 92 month (7.5 years) sentence after pleading guilty to comparable fraud and money laundering charges.
In addition to their prison sentences, the two individuals were also ordered to forfeit hundreds of thousands of dollars as part of the court’s judgment. After completing their time in custody, they will be required to serve a term of supervised release, during which they must comply with specific conditions set by the court.
This case is an example of a broader crackdown by United States authorities targeting North Korea’s aggressive use of cyber fraud to obfuscate sanctions and generate revenue.
Officials warn the tactics used in this scheme, particularly the exploitation of remote hiring processes is the growing attack surface for organisations worldwide.