SYDNEY, 25 August 2022 – Bitdefender has released key data from its August Bitdefender Threat Debrief (BDTD), a monthly series analysing threat news, trends, and research from the previous month.
Ransomware
As part of Debrief, Bitdefender released a Ransomware Report which analysed malware detections collected in July 2022 from its static anti-malware engines. The report looks at ransomware detections, rather than infections, and counts total cases, not how monetarily significant the impact of infection is.
It identified 205 ransomware families in July, with the number of detected ransomware families varying each month depending on the current ransomware campaigns in different countries. WannaCry was the most widely detected ransomware family, accounting for 37 per cent. Robin came in second at 20 per cent.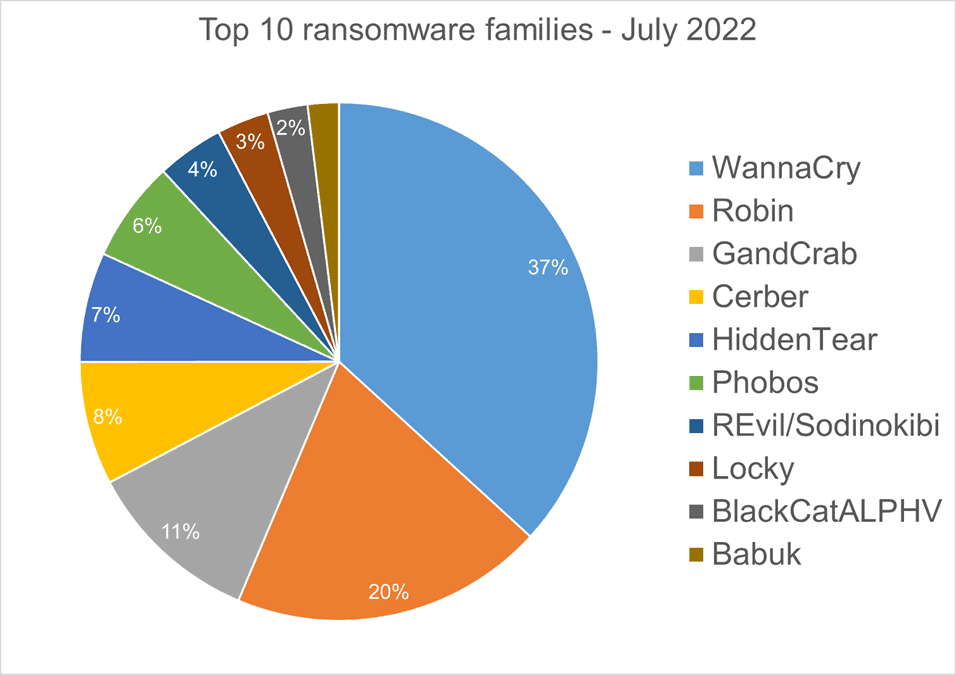
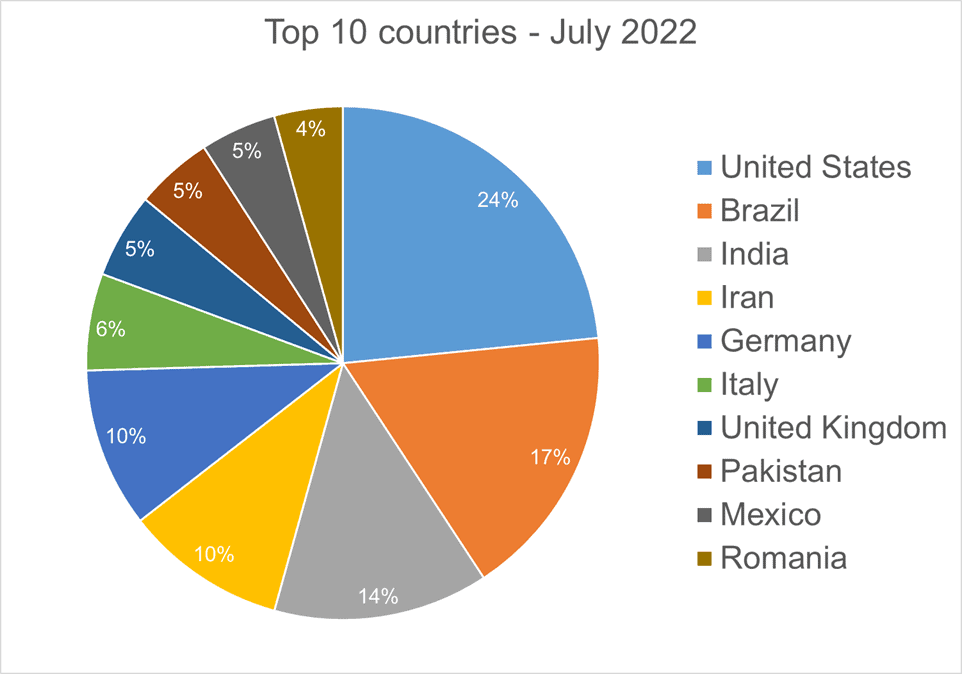
In total, the company detected ransomware from 151 countries in its dataset this month as ransomware continues to be a threat that touches almost the entire world. Many ransomware attacks continue to be opportunistic, and the size of population is correlated to the number of detections. The United States was the most impacted by ransomware, accounting for 24 per cent, followed by Brazil at 17 per cent and India at 14 per cent.
Android Trojans
The global cybersecurity solutions company also analysed the top 10 trojans targeting Android the company has seen in its telemetry during July.
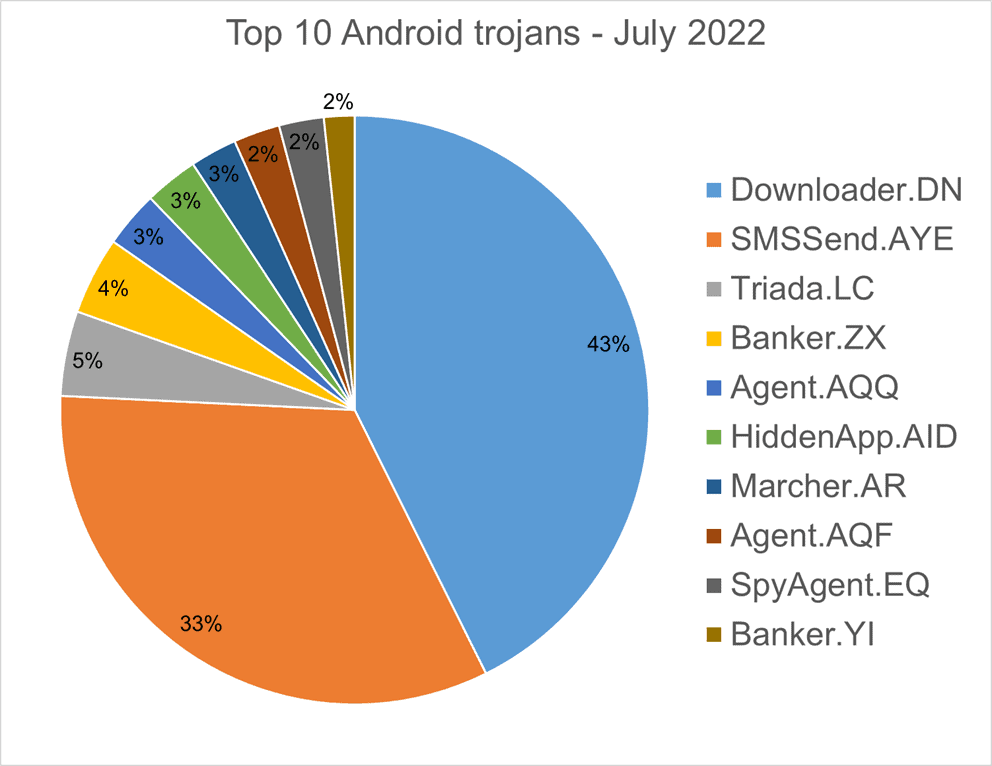
Downloader.DN – repacked applications taken from Google App Store and bundled with aggressive adware – was the biggest trojan targeting Android at 43 per cent, followed by SMSSend.AYE – malware that tries to register as the default SMS application on the first run by requesting the user’s consent of the user – at 33 per cent.
Homograph Attacks
Bitdefender analysed homograph attacks, which work to abuse international domain names (IDN). Threat actors create international domain names that spoof a target domain name. A ‘target’ of IDN homograph phishing attacks refers to the domain that threat actors are trying to impersonate.
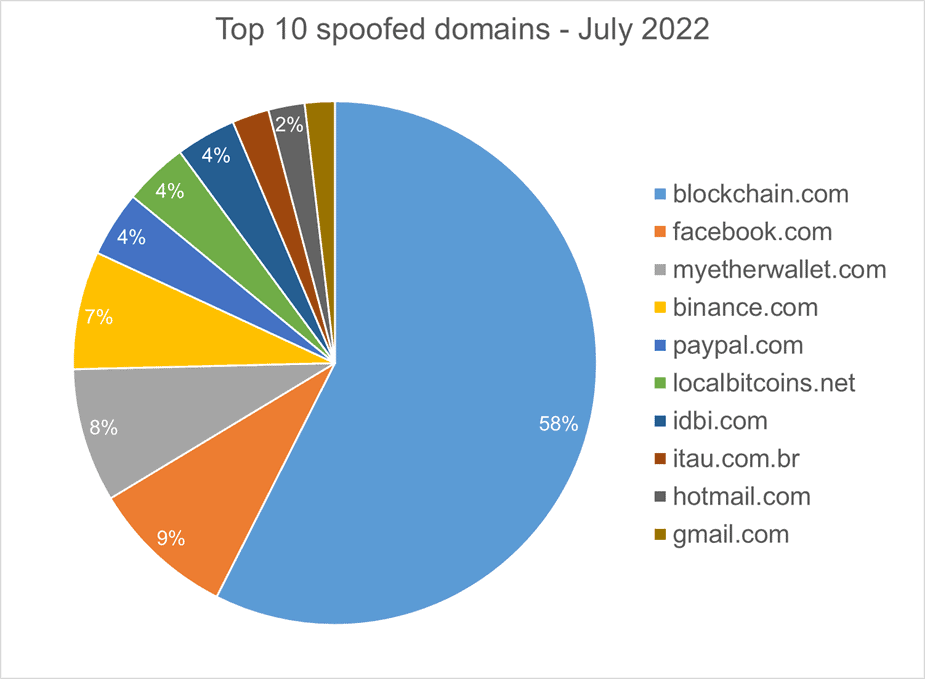
Blockchain.com was by far the most common target, accounting for 58 per cent of attacks, with facebook.com, binance.com, paypal.com, and gmail.com among the other targets.
To access the full report, see here.
##
About Bitdefender
Bitdefender provides cybersecurity solutions and advanced threat protection to hundreds of millions of endpoints worldwide. More than 150 technology brands have licensed and added Bitdefender technology to their product or service offerings. This vast OEM ecosystem complements telemetry data already collected from our business and consumer solutions. To give you some idea of the scale, Bitdefender Labs discover 400+ new threats each minute and validate 30 billion threat queries daily. This gives us one of the industry’s most extensive real-time views of the evolving threat landscape.