Cyber threats have moved to mobile communications, where identity, metadata exposure, and AI impersonation undermine trust.
The Voice of Cyber®
Encryption & Cipher
Encryption is a fundamental aspect of cybersecurity, particularly in the context of protecting sensitive information from unauthorised access. Encryption involves the use of algorithms to convert plaintext data into ciphertext, rendering it unreadable without the appropriate decryption key. This process ensures the confidentiality and integrity of data during transmission or storage. Cipher, on the other hand, refers to the specific algorithm or method used for encryption and decryption.
Newest Release
No results found.
Deep Dive Articles
Sort By
- Date
- Title

Today’s Digital Landscape
Metadata is one of the most overlooked security risks in modern digital communications. Adversaries no longer need to break into encrypted chats to ...

In government and critical infrastructure, security is not an optional feature, it is the foundation of operational integrity. For organizations responsible for protecting ...
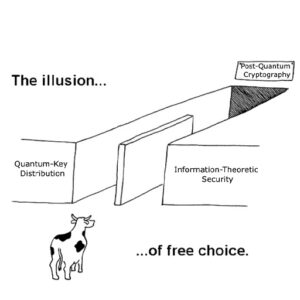
Every few months, another “quantum-safe” technology is marketed as the real answer, usually with the claim that post-quantum cryptography isn’t enough. PQC is too new, ...

Introduction
Australia is standing at the edge of a technological shift that could redefine cyber resilience. With quantum computing on the horizon, the very foundations of ...

How New Certificate Lifecycle Standards Are Set to Prepare the Business Landscape for a Quantum Ready Future

Artificial intelligence (AI) is revolutionizing cryptanalysis, making traditional symmetric key encryption increasingly vulnerable. AI-driven differential and sectional ...
No results found.
In The News
Sort By
- Date
- Title
New service helps organisations identify cryptographic vulnerabilities and build scalable post-quantum strategies
WATERLOO, ONTARIO – October 9 – BlackBerry Limited (NYSE: BB; TSX: BB) today announced the expansion of BlackBerry® SecuSUITE® to Windows® devices, extending sovereign-grade ...
FortiOS features empower organisations to safeguard highly sensitive data from quantum threats, migrate to post-quantum security, and future-proof their infrastructure with ...
Other key findings show an increase in crypto miner detections, a spike in zero-day malware, a drop in endpoint malware, a rise in Linux-based threats, and more.

Melbourne, Australia, April 2025 - ExeQuantum, a cybersecurity company specializing in post-quantum cryptography, has officially launched a production-ready implementation of ...

Melbourne, Australia & Dubai, UAE – March 2025 – ExeQuantum, a leader in Post-Quantum Cryptography (PQC) solutions, has officially partnered with CyberWaze, a global ...
No results found.
Podcasts On Encryption & Cipher
No results found.
No results found.
