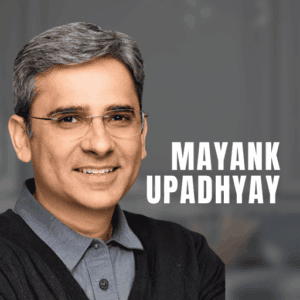
Snowflake has recently appointed Mayank Upadhyay its Chief Security and Trust Officer to lead security efforts.
Mayank brings one of the most influential careers in enterprise security to Snowflake. During his more than two decades at Google, he shaped the modern security landscape, ultimately serving as Vice President of Engineering for Google Cloud where he secured both the public-facing Google Cloud Platform and the private cloud infrastructure powering core Google services. Prior to this, his career progression to Distinguished Engineer was defined by a sequence of foundational technologies he delivered.
Today, as CSTO at Snowflake, he secures the data and AI foundation for 11,000+ customers ...